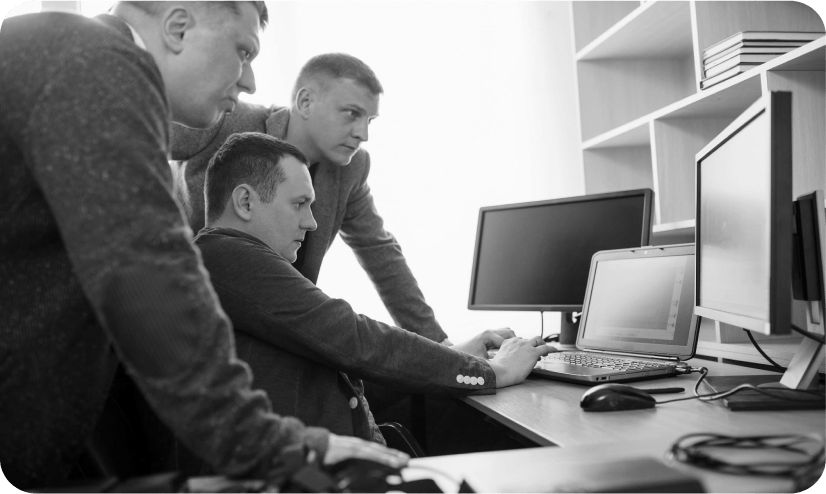
Accomplish more with resilient IT
Experience the power of UDT’s fully integrated IT services, products, and expertise designed for you.
Enterprise technology solutions and IT insights aligned to your most important digital strategies
Conectivity Communications
Revolutionize your network strategy with UDT Connectivity Solutions
There’s a lot riding on the reliability and success of your Internet connection and networking solutions. UDT’s resilient, secure, and flexible services empower organizations to thrive without interruption.

Consulting
Gain comprehensive technology expertise with UDT’s IT Consulting Services
Every organization needs a tailored, technology roadmap. UDT Consulting Services lead to optimized IT environments that support key initiatives, foster functionality, and drive successful, strategic digital transformation.

Cybersecurity Services
Experience smart, simple security with UDT Cybersecurity Services
Technology alone is not going to solve your security problems. UDT’s proven holistic approach pinpoints the key areas where we need to act first to make the most impactful improvements to your overall security posture.
Lifecycle Management
Optimize operations and performance with UDT Lifecycle Services
As a cross-OEM certified and OS-agnostic provider, UDT is equipped to deliver complete, custom endpoint management solutions that support your goals for digital sustainability while ensuring a seamless experience.

Managed Services
Achieve efficient IT operations and support with UDT’s Managed IT Services

Professional Services
Optimize IT and develop your technology roadmap with UDT’s IT Professional Services
UDT has the people, technology, and resources to offer efficient, secure, and dependable IT. We’ll fill the gaps in your IT systems and processes while reducing the workload on your team with seamless, 24/7 support.

More than 700 partners to help you accomplish more
Deep expertise for full-coverage IT
Cloud
Empower modern organizations with performance and security.
Network Infrastructure
Put the customer first with secure, reliable network connectivity.
Data Center Infrastructure
Empower efficient and secure IT with scalability, & performance.
Digital Classroom
Designed to support sustainable and equitable learning.
Digital Workspace
Achieve more with enhanced productivity and collaboration.
Outcomes
Your outcomes, our solutions

Manage Resources

Enhance Experience
Grow Revenue
Streamline Operations

Mitigate Risks
Industries
IT solutions designed for your industry
K12 Education

Financial Services
Commercial Business

Hospitality

State & Local Government
Higher Education
Insights that Empower
Explore our suite of expert resources, client case studies, and partner collaborations, designed to educate, connect, and empower the strategic management of your IT systems, operations, and end-user experiences.
Private AI Sovereignty: How to Secure the Corporate Brain
Kingsport school board cuts internet expenses by a projected $28,000 annually
The Lifecycle Loop: Why “Run Until It Breaks” is the Most Expensive IT Strategy
UDT Featured in Latino Leaders Magazine’s Index 500 as a Leading Latino-Owned Company
The Cybersecurity Insurance Gap: Is Your Infrastructure Still Insurable?
The Invisible Drain: Quantifying the True Cost of IT Downtime
From Endpoint to Identity: Why Cybersecurity Strategies Are Converging
Managed IT vs. Co-Managed IT: Choosing the Right Support Model for 2026
UDT Awarded HP Partner of the Year for 2025
Your Microsoft 365 License Needs a Cybersecurity Strategy
Careers
Grow your career with us
Join a flexible, hybrid-friendly work environment with career-changing opportunities. We welcome experienced and aspiring tech professionals across every discipline and business function.

Get your personalized IT action plan
UDT is committed to your success. We’ll connect you with the right IT solutions for your unique needs and challenges.
Contact us today.
-
2900 Monarch Lakes Blvd, Suite 300
Miramar, FL 33027
